SOC 2 compliance demonstrates that your organization has strong controls in place to protect customer data—focusing on security, availability, processing integrity, confidentiality, and privacy (known as the Trust Services Criteria or TSC). For smaller businesses like many of our clients, it's often a key requirement to win enterprise contracts, meet cyber insurance needs, or build trust with partners. It's not a "certification" but an independent auditor's report (issued by a CPA firm) attesting to your controls.
The good news? You don't have to tackle this alone. As your managed service provider (MSP), BizCare can  simplify the process significantly by handling technical controls, evidence collection, policy implementation, and ongoing monitoring—turning what feels overwhelming into a clear, manageable roadmap.
simplify the process significantly by handling technical controls, evidence collection, policy implementation, and ongoing monitoring—turning what feels overwhelming into a clear, manageable roadmap.
Key Differences: SOC 2 Type 1 vs. Type 2
- Type 1: A "point-in-time" snapshot. It evaluates whether your controls are designed properly as of a specific date. Faster and less expensive—ideal for a first-time effort or when you need to show progress quickly.
- Type 2: Examines both design and operating effectiveness over a period (typically 3–12 months, often 6–12 for stronger assurance). This is what most clients and prospects expect long-term, as it proves controls actually work in practice.
Many organizations start with Type 1 and move to Type 2 the following year.
Recommended Step-by-Step Preparation Process
Here's a practical roadmap tailored for smaller organizations. Typical timeline: 3–6 months for Type 1 readiness; 6–12+ months for full Type 2 (including the observation period).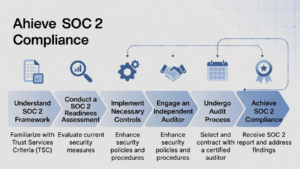
- Define Your Objectives and Scope Clarify why you need SOC 2 (e.g., client requirements, insurance, risk reduction). Decide which TSC to include—Security is always required; add others (Availability, Confidentiality, etc.) based on your services and customer needs. Identify the "system" in scope (e.g., specific applications, cloud environments, or your full IT infrastructure handled by BizCare).
- Assemble a Small Internal Team Include key stakeholders (e.g., leadership, IT contact). We'll work closely with you as your extension—assigning control owners and coordinating efforts.
- Conduct a Gap Assessment / Readiness Review Review your current policies, procedures, and technical controls against the TSC. Identify gaps (e.g., access controls, incident response, logging). BizCare can lead or support this using our tools and expertise—leveraging existing services like Multi-Factor Authentication (Duo), endpoint protection, backups, and monitoring.
- Develop or Update Policies and Controls Create or refine documents such as: acceptable use policy, incident response plan, access control procedures, risk assessment, and data handling guidelines. Implement technical controls (e.g., MFA everywhere, logging/monitoring, patch management, encryption). Our Advanced Security 2026 package and Managed CoPilot AI (with guardrails) directly support many of these.
- Implement, Test, and Gather Evidence Put controls into daily operation. Collect evidence (logs, screenshots, access reviews, training records). For Type 2, this runs over the audit period. We handle much of the heavy lifting—automated monitoring, quarterly reviews, and evidence export from our platforms.
- Perform a Readiness Assessment A pre-audit dry run to fix issues early. This reduces surprises and costs during the formal audit.
- Engage an Independent Auditor Select a reputable CPA firm experienced with smaller businesses. They'll perform the formal examination and issue the report. BizCare can recommend trusted partners and help prepare documentation to streamline their work.
- Remediate, Audit, and Maintain Address any findings, complete the audit, and receive your report. Then shift to continuous compliance (annual renewals are standard).
How BizCare Makes This Easier and More Valuable for You
We align directly with your Risk Intelligence and Countermeasures (RIC) Master Plan:
- Stabilization and IT Foundation provide the baseline (patching, backups, endpoint protection).
- Advanced Security 2026 covers critical controls like MFA (Duo), XDR, Microsoft 365 hardening, password vaults, dark web monitoring, and zero-trust measures.
- Managed CoPilot AI adds guardrails for safe AI use—addressing modern risks like shadow AI and data leakage.
- Our vCSO and ongoing support help with policies, training, incident response, and evidence for audits.
- Email Security and Cisco Umbrella add layers for phishing protection and DNS-level threat blocking—strengthening Security and Confidentiality criteria.
Many controls we already manage can reduce your scope or serve as "subservice organization" evidence, lowering your effort and cost. We also deliver security awareness training and can support third-party risk assessments.
Realistic Timeline and Investment Considerations
- Timeline: Type 1 can often be achieved in 2–4 months with focused effort. Type 2 requires the operational period, so plan for 6–12 months initially.
- Costs: For smaller organizations, expect $20,000–$80,000 total in the first year (including readiness help, tools, and audit fees). Ongoing annual costs are typically lower. Automation and MSP support (like ours) can significantly reduce this by minimizing manual work.
The return often comes quickly through faster sales cycles, stronger client trust, and reduced risk of breaches or insurance issues—especially amid rising AI-powered threats and regulations.
We're here to empower you with clear visibility and confidence at every step, without the technical overwhelm. If this aligns with goals in your RIC Master Plan or addresses concerns around governance and cybersecurity, let's schedule a quick call to tailor the next actions to your environment—whether that's a gap assessment, policy review, or scoping discussion.


You must be logged in to post a comment.