 SOC 2 compliance does not have a strict list of "required" CIS Controls. SOC 2 is based on the AICPA Trust Services Criteria (TSC) — primarily the Security criterion (which is mandatory), with optional additions like Availability, Confidentiality, Processing Integrity, or Privacy depending on your clients' needs.
SOC 2 compliance does not have a strict list of "required" CIS Controls. SOC 2 is based on the AICPA Trust Services Criteria (TSC) — primarily the Security criterion (which is mandatory), with optional additions like Availability, Confidentiality, Processing Integrity, or Privacy depending on your clients' needs.
CIS Controls (v8 or v8.1) serve as practical, technical guidance to help you design and implement the controls that satisfy SOC 2 requirements. They are not mandatory, but they map very well to SOC 2 and are widely used by organizations (including smaller ones) to build auditable, effective security programs.
Why CIS Controls Help with SOC 2
- CIS Controls provide specific, prioritized actions (18 high-level controls with hundreds of safeguards) that address the "how" of security.
- SOC 2 focuses on the "what" — proving through evidence that your controls are suitably designed and operating effectively over time.
- Official mappings from the Center for Internet Security (CIS) show strong alignment, especially with the Security TSC (Common Criteria CC1–CC9).
For many smaller organizations, implementing Implementation Group 1 (IG1) of CIS Controls covers roughly 70% of the technical requirements for a SOC 2 Security report. Adding key IG2 safeguards (such as centralized logging, vulnerability scanning, and penetration testing) can bring coverage to about 90%.
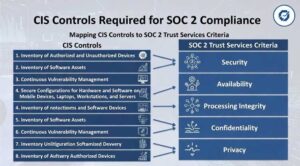
Key CIS Controls That Commonly Support SOC 2
Here are the most relevant CIS Controls (v8/v8.1) and how they typically map to core SOC 2 areas:
- CIS 1: Inventory and Control of Enterprise Assets Helps with knowing what you need to protect (supports risk assessment and asset management in SOC 2).
- CIS 2: Inventory and Control of Software Assets Ensures you track authorized software (ties into access and change management).
- CIS 3: Data Protection Covers encryption, classification, and secure handling — directly supports Confidentiality and Privacy TSCs.
- CIS 5: Account Management & CIS 6: Access Control Management Critical for logical access controls (CC6 in SOC 2) — one of the most common areas of audit findings.
- CIS 7: Continuous Vulnerability Management Supports risk assessment and system hardening.
- CIS 8: Audit Log Management Enables monitoring, anomaly detection, and incident response (CC7).
- CIS 10: Malware Defenses Helps meet requirements for preventing malicious code.
- CIS 12: Network Infrastructure Management & CIS 13: Network Monitoring and Defense Support secure configurations and detection.
- CIS 17: Incident Response Management Essential for handling security events.
- CIS 18: Penetration Testing (often IG2+) Helps validate controls.
Other supportive controls include secure configuration (CIS 4), secure development (CIS 16), and physical security where applicable.
How BizCare Can Help You Align CIS Controls with Your SOC 2 Journey
As your MSP, we already deliver many of these foundational elements through your Risk Intelligence and Countermeasures (RIC) Master Plan:
- Stabilization & IT Foundation — Handles asset inventory, patching, backups, and basic endpoint protection (aligns with CIS 1, 7, 10).
- Advanced Security 2026 — Includes MFA (Duo), XDR, Microsoft 365 hardening, password vaults, dark web monitoring, zero-trust whitelisting, and firewall controls (strongly supports CIS 5, 6, 8, 12, 13).
- Managed CoPilot AI — Adds guardrails for safe AI use, data mapping, and blocking unsafe apps (helps with data protection and modern risks in Confidentiality/Privacy).
- Ongoing services like security awareness training, incident response planning, and evidence collection make it much easier to demonstrate operating effectiveness during a SOC 2 audit.
We can perform a gap assessment that maps your current environment (and our managed services) directly to both SOC 2 TSC and relevant CIS Controls. This helps prioritize quick wins, reduces duplication of effort, and keeps things simple and cost-effective for your team.
Practical Next Steps for You
- Decide your SOC 2 scope (Security only, or additional TSCs) and timeline (Type 1 vs. Type 2).
- Review the official CIS-to-SOC 2 mapping (available as a free download from cisecurity.org — we can walk through it with you).
- Let us run a lightweight readiness review against your current setup and our services.
- Build or refine policies and evidence collection — we handle much of the technical heavy lifting.
This approach turns compliance from a checkbox exercise into a real security and trust advantage — especially important for smaller businesses facing AI-related threats, client demands, and insurance requirements.
We're here to empower you with clear visibility and confidence at every step, without the technical overwhelm. If this aligns with goals in your RIC Master Plan or addresses concerns around governance and cybersecurity, let's schedule a quick call to tailor the next actions to your environment—whether that's a gap assessment, policy review, or scoping discussion.


You must be logged in to post a comment.