When it comes to technology, the methods employed by cybersecurity administrators have evolved as rapidly as the users and smart-devices themselves. Modern cybersecurity professionals can all relate - certainly those who practice Good Cyber Hygiene over their internet of things day-to-day. Enabled with identity profiles and compliance policies that in-turn permit secure access to critical and private business information users, devices, applications, and services are continuously autonomously curated within milliseconds. Privileged access is permitted or denied on a large scale — defending your network, devices, and community.
LOCK YOUR FRONT DOOR: THE NETWORK
The network provides the first level of protection against BYOD devices a lot of the time. It is the first thing users with outside devices commonly will connect to upon arrival. Proper segmentation of the network is a basic way to provide security to the network when dealing with BYOD devices. This can include firewalls or network access lists to control what these outside devices are able to access. Short, sweet, and to the point. This is a basic way that some companies choose to handle BYOD devices. They simply give these devices web access and restrict access to internal company resources.
What happens the first time a vendor comes on-site and needs access to your network to fix a device or an application though? You will not have control of their device, nor will a simple internet connection suffice. They will need permissive, yet secure access to the internal network in one way or another. In terms of the network, device profiling can allow both wired and wireless network users to get an individualized access control list based on their user credentials or device, for starters.
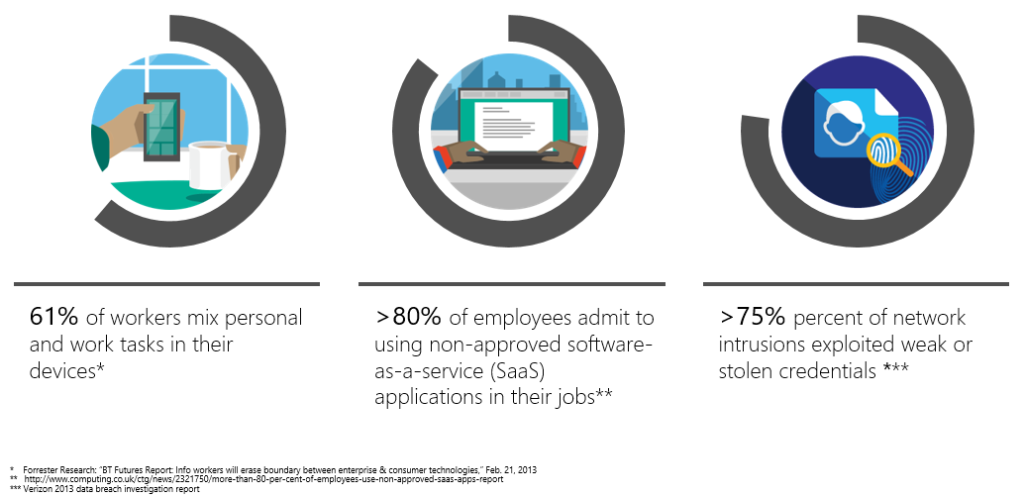
PATROL YOUR BYOD DEVICES: SERVICES AND SOFTWARE
BYOD devices can be of many different brands and models, and with that, they carry a wide range of software as well. Some of these devices are more secure than others. The goal is the same: to keep the internal systems and applications secure. This is often accomplished with device posturing. Device posturing is the process of ensuring that devices that come on to the network are up to predetermined system security standards. If they are not, they will not be allowed to connect. Your network administrator is responsible for ensuring that all devices on their watch are up to date with the latest security updates, as well as free of malware. Device posturing ensures the security standards are upheld, not only by company employees with corporate assets, but also visitors bringing their own devices onsite.
DEFEND YOUR COMMUNITY: PRIVILEGED ACCESS
The third and often neglected cybersecurity challenge concerns the BYOD users themselves. Typically, access to internal systems is gated through subnetworks, for example, wireless, or VLAN networks. At the most basic level of security, users are routed to subnetworks that commonly share a similar set of firewalls rules and permissions. Moving it one step higher, users are permitted access to resources contingent on membership specified by security policies. For example, the team a user is working on, or an application they are assigned to support. Taking it still a step higher, users can be permitted access to resources based on individual access policies that can work on a per-user basis. In all three methods, the common theme is that users are only permitted access to required resources, and nothing more.
Those three topics are some of the common things that come up when the conversation of BYOD is mentioned. Discussing and developing a plan around these things will ensure that you are putting the needed focus on such a sensitive topic. While this is not a guide for BYOD devices in your network, these three areas of focus will be a good start to securing BYOD devices in your IT environment.


You must be logged in to post a comment.