Passwords are an inherently flawed security measure in an era of constant phishing attacks and massive data leaks. This guide breaks down the latest ...
Enterprise
BizCare, Inc.
MAEW PATCHARANUN
Modern password tips based on NIST guidelines
BizCare, Inc.
BIZCARE, INC
What are the CIS controls are required for SOC 2 compliance
SOC 2 compliance does not have a strict list of "required" CIS Controls. SOC 2 is based on the AICPA Trust Services Criteria (TSC) — primarily the Security ...
BizCare, Inc.
MAEW PATCHARANUN

Not all hackers are criminals: A look at the three major hacker types
While the term “hacker” often dominates cybersecurity conversations, it’s crucial to recognize that not all hackers share the same motivations. ...
BizCare, Inc.
MAEW PATCHARANUN

The hidden weaknesses of multifactor authentication
Multifactor authentication (MFA) works by requiring users to provide more than one form of identification when logging into a system or account. This ...
BizCare, Inc.
MAEW PATCHARANUN

2026 Cybersecurity trends and predictions
Cybersecurity experts Rob Wright (Dark Reading), David Jones (Cybersecurity Dive), and Alissa Irei (TechTarget Search Security) recently came together ...
BizCare, Inc.
MAEW PATCHARANUN

Tips for creating more secure business passwords
Strong passwords are one of the easiest and most effective ways to protect online accounts. Still, many businesses use weak or reuse credentials. Learning ...
BizCare, Inc.
MAEW PATCHARANUN

Beyond hackers: Why your most trusted employee might be your biggest risk
We give our IT teams the keys to the kingdom to keep operations running. Yet, that access creates a massive blind spot. Recent trends show disgruntled ...
BizCare, Inc.
MAEW PATCHARANUN

Rolling out zero trust security the right way
With cyberthreats escalating and major breaches costing billions, many organizations are embracing the zero trust approach, a holistic methodology that ...
Small Business
BizCare, Inc.
BIZCARE, INC
What keeps smaller business owners up at night when it comes to AI, Governance and Cybersecurity
At BizCare, we're a technology solution company uniquely focused on driving business outcomes. We enable our clients—smaller organizations that view ...
BizCare, Inc.
BIZCARE, INC
SEC’s Cybersecurity Risk Management Rules for Funds and Advisers
The Securities and Exchange Commission (SEC) has introduced updated cybersecurity risk management rules, initially proposed in February 2022. These ...
BizCare, Inc.
BIZCARE, INC
The SEC’s 2023 Cybersecurity Initiatives: New Rules for Enhanced Security
In 2023, the U.S. Securities and Exchange Commission (SEC) reaffirmed its focus on data security, cybersecurity, and IT operational resilience. The SEC ...
BizCare, Inc.
BIZCARE, INC
How cyber-resilience goes beyond cybersecurity
We empower security-focused organizations and their supply chains to achieve true cyber-resilience through a bold, all-encompassing approach that transcends ...
BizCare, Inc.
PARTNERS
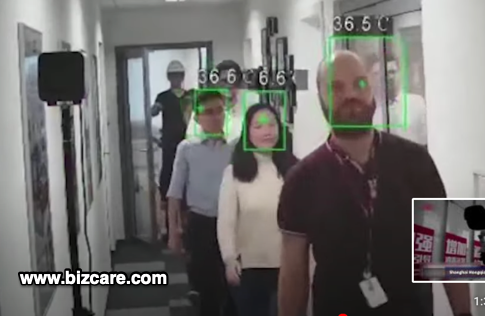
A.I. Powered Crowd Thermal Monitoring Solution Launched by BizCare® Helps Hospitals Education and Businesses
News provided by BizCare
Lafayette, CA., April 7, 2020 -- BizCare recently released its new Crowd Thermal Monitoring Solution which helps organizations ...
BizCare, Inc.
PARTNERS
Best Practices for Managing Remote Teams
In the past week, we've received several inquiries about managing remote staff. As companies around the globe grapple to address coronavirus and ...
BizCare, Inc.
BIZCARE, INC

How to use Twitter to grow your business
Twitter is one of the most popular social media platforms for businesses because it enables them to focus on public conversation and exposure. Businesses ...
BizCare, Inc.
BIZCARE, INC

4 Biggest Facebook marketing mistakes
Facebook makes it possible for companies to showcase their products and services to targeted prospects more effectively and take their online presence ...
